Cybersecurity
The Inside Story of Tor, the Best Internet Anonymity Tool the Government Ever Built
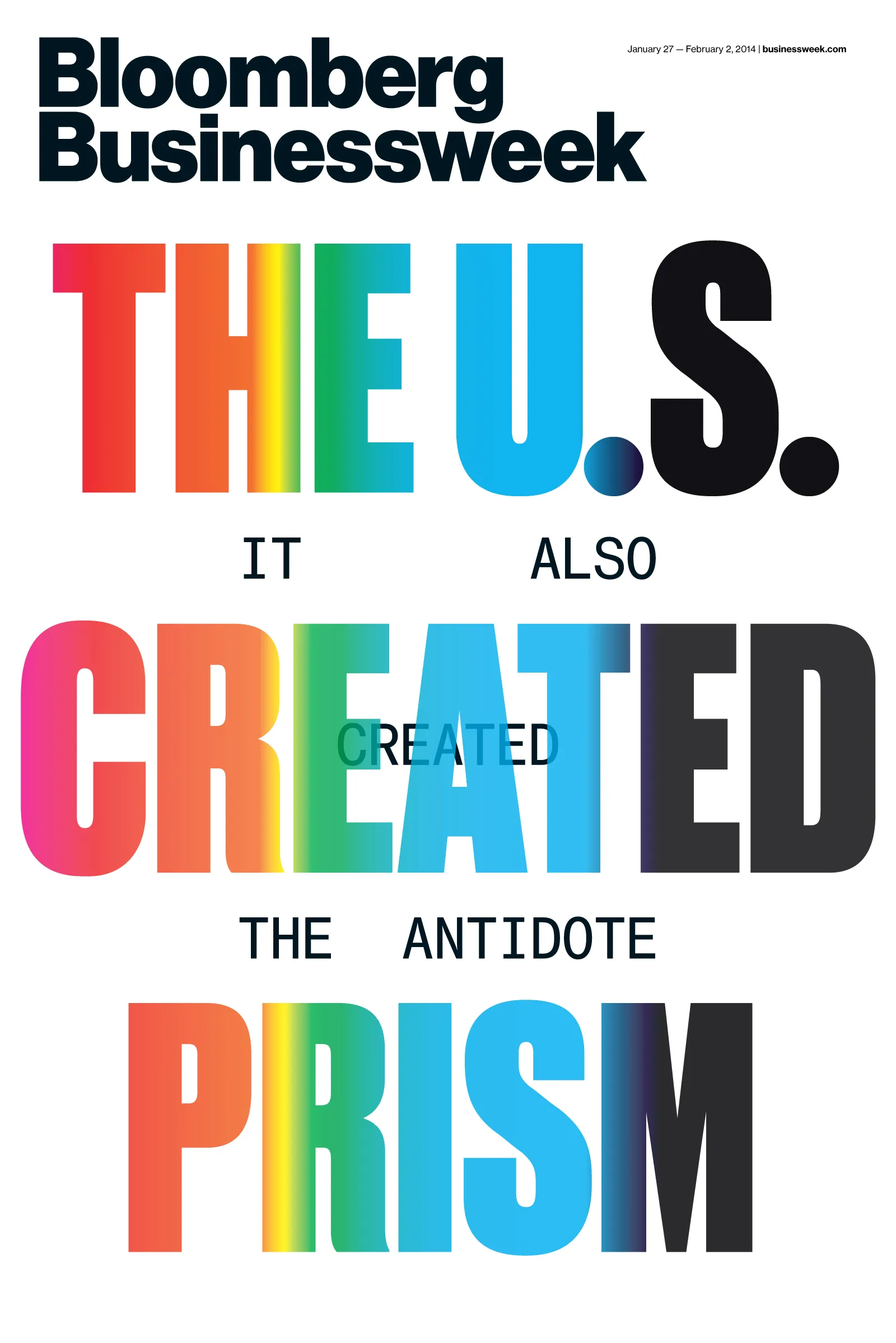
The U.S. government designed and funds the best defense against its own surveillance
This article is for subscribers only.
Last year, Edward Snowden turned over to the Guardian, a British newspaper, some 58,000 classified U.S. government documents. Just a fraction of the files have been made public, but they outline the National Security Agency’s massive information-collection system. They’ve thrown light onto the methods of an arm of the government used to working in the shadows and started an intense debate over national security and personal liberty. One of the earliest and most explosive revelations was the existence of Prism, a top-secret program giving the NSA direct access to the systems of Google, Facebook, and other U.S. Internet companies.