The Big Hack: The Software Side of China’s Supply Chain Attack
It wasn’t just hardware. An online portal for firmware updates hid and distributed malware.
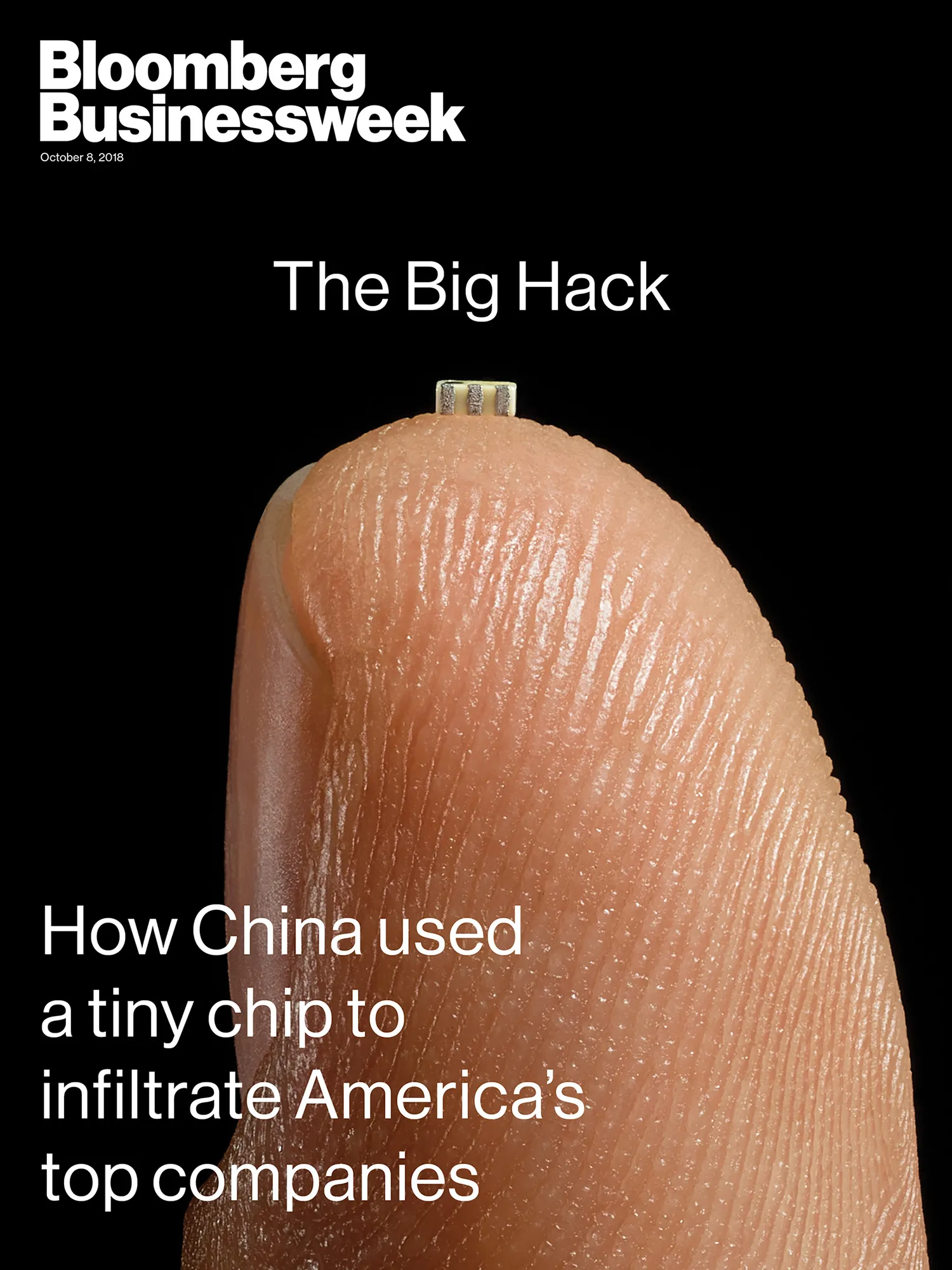
Even as Amazon, Apple, and U.S. officials were investigating malicious microchips embedded in Supermicro server motherboards, Supermicro was the target of at least two other possible forms of attack, people familiar with multiple corporate probes say.
The first of the other two prongs involved a Supermicro online portal that customers used to get critical software updates, and that was breached by China-based attackers in 2015. The problem, which was never made public, was identified after at least two Supermicro customers downloaded firmware—software installed in hardware components—meant to update their motherboards’ network cards, key components that control communications between servers running in a data center. The code had been altered, allowing the attackers to secretly take over a server’s communications, according to samples passed around at the time among a small group of Supermicro customers. One of these customers was Facebook Inc.